The Internet as our Nervous System: from Cloud to Local-first
Imagine for a moment that you, and all of the people around you, are single neurons.
Where it all starts
Imagine for a moment that you, and all of the people around you, are single neurons. Throughout most of human history, we could only talk to other neurons close to us via 'synapses' of a spoken language.
With the invention of writing, we discovered the possibility to connect all of these neurons. Our speed of communication was slow and the messages we transmitted were few. Sometimes, it took centuries for some transformative ideas like Arabic numerals or heliocentrism to travel across the globe. Still, we solitary neurons became globally connected for the first time.
With the invention of the telegraph, telephone, radio and television, the speed and quality of our connections improved vastly. Our shared network became stronger and more diverse in its messages.
The Internet as our superpower
Then came the Internet - the quintessence of interconnectedness. More than any other time in human history, most of us are connected to the nervous system of humanity.
Many of us spend most of our waking hours on the Internet. We can broadcast what we think and feel, communicate with other neurons, and co-create intricate webs of cooperation. We can think of this digital nervous system as our collective superpower.
The internet is built as a great foundation for this nervous system. It is decentralized by design - no single party controls it.
The cloud and its limitations
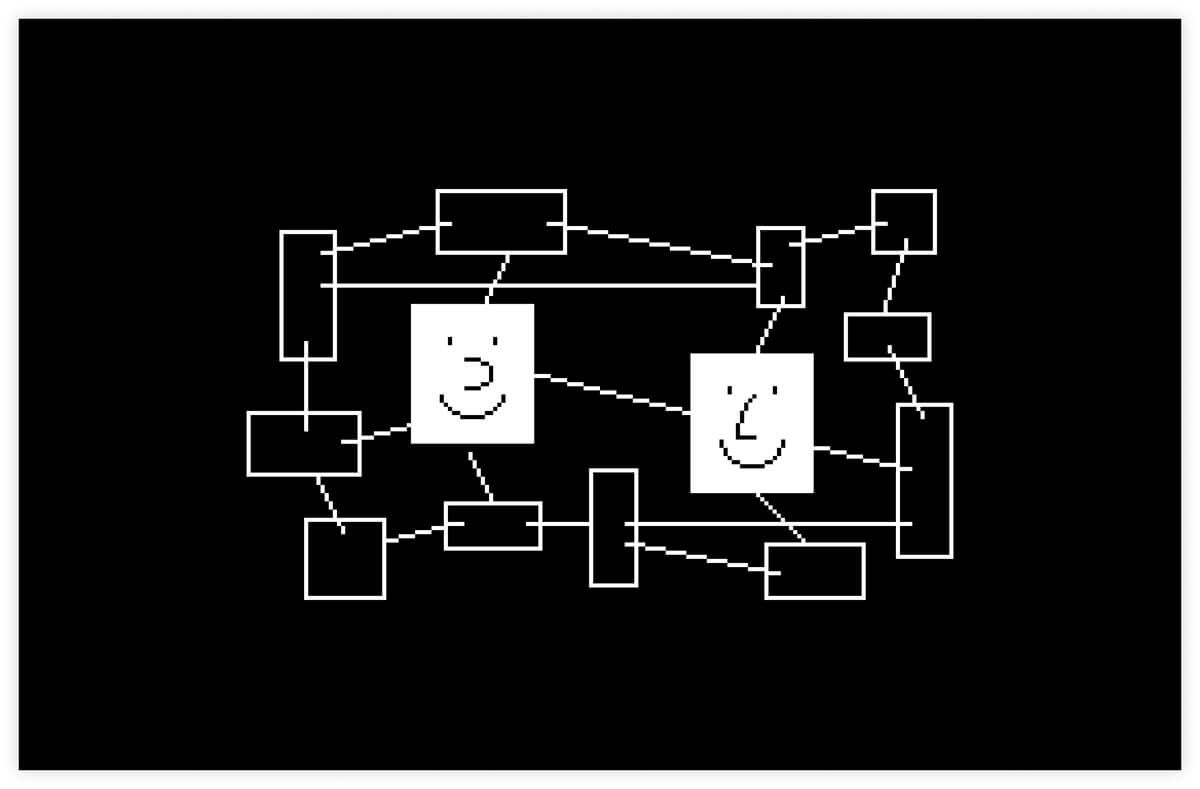
Cloud-based architecture: where application developers are the keepers of our keys
The problem is that the modern Internet relies strongly on cloud technologies, where client applications communicate with each other only via servers. It is akin to having a server between any two neurons in the nervous system, or each neuron being inside a box that decides if the signal from this neuron can go through.
In cloud architecture, application developers store keys of the accounts of users on their behalf, so they are the keepers of keys. It means that these applications now hold the power to voice down some and promote others, to block and to recommend, to decide which information is shared and distributed on the Internet. Software companies can block people based on their geographic location, based on random algorithms, personal beliefs of their founders or shareholders, and the political agenda of powerful groups they are close to.
In some sense, we now have even different parts of these nervous systems loosely connected. The Western internet. The Chinese internet. The Russian internet. The Iranian internet. And so on. They look different, but underneath there is the same structure of power - different elites with different agendas control how neurons talk, what information they see and if they can communicate at all.
This separateness is not the biggest problem; what is more dangerous is that in each of these versions of the Internet, the neurons can’t talk and express themselves directly to each other. Servers control our communication with those closest to us: family members, neighbors and local communities.
The problems with cloud-based architecture don't stop there. Not only do central servers control who can do what, but their control is ubiquitous. Even when texting your family member on the couch next to you, the signal from your device to theirs needs to go to the application server first, and only after that, return to your own living room.
If that center fails or does not respond, it means that even nearby neurons cannot communicate digitally. For a biological organism, an unresponsive nervous system would mean an instant death. The nervous system of humanity needs an upgrade.
A no-one in between nervous system
Anytype: A no-one in-between network
There are parts of the Internet where server-first architecture is more efficient - massive online games, uber-like networks and other examples. For the role the communication layer plays, we can use a better approach than the cloud.
If we are to design a nervous system that's resilient and agile, it needs a different wiring - when neurons connect to each other directly. For this we need to give the keys to neurons and wire them differently - on local first principles. This wiring we call a “no-one in between” communication system.
A no-one in between wiring is a better foundation for families, communities and associations of creators.
How to implement. Technological foundation.
Two pieces of technology look striking, especially if we imagine their combined power. These technologies come under the obscure names of Public Key Cryptography and CRDTs.
Public key cryptography can protect digital data in a way that is not possible in the world of atoms. Imagine each of us having a vault that no one in the whole world can break into. Not a malicious hacker, not a powerful state, not even if they combined forces. This is not possible in the world of atoms.
By using public key cryptography, we can generate your very own vault where your data and messages live, and which has two keys: private and public. Knowing your public key, anyone can send encrypted messages but only you - the holder of the private key - can open the vault and see what's inside. All of the computational resources on Earth are not enough to decrypt a single message. Generating such keys does not cost any money and can be done on any computer, without the need to connect to the internet. Vault creation and authorization can be fully independent from anyone. It means each neuron can be digitally independent.
Once we have our independent vaults from which we control the keys, we can also enable vaults to talk to each other on local-first principles. This is where CRDTs come in.
In traditional cloud architecture (also known as client-server), all clients need to connect to a server where the master record is kept. This server resolves potential conflicts when clients are working on the same information, especially in real time.
If we want to change the wiring to local first, we need a way to resolve conflicts independently by all clients, so that the client is not dependent on a server for this. This is not easy as we cannot control which devices are online, which are offline.
Fortunately, there is a new piece of technology called CRDTs (conflict-free replicated data types) that allow reaching the same state irrespective of the order in which changes are received, so each device can resolve conflicts independently - without relying on a single master copy.
Public key cryptography has been implemented widely. So far mostly in crypto wallets. CRDTs on the other hand is a fresh approach that emerged in computer science in 2011 and has mostly been implemented in experiments and research.
The implementation
That’s why our team at Anytype has been working on combining both approaches into a new local first protocol based on creators’ keys. It is called AnySync and it supports hi-performant and scalable synchronization of objects, discussions, communities and apps that do not depend on a cloud. You can read more about our sync protocol here.
Anytype is an interface to vaults, described in this article - encrypted, local first and with keys controlled by creators. This means in Anytype there's nobody standing between you and your vault, you and your contacts, or your devices and each other, and that these vaults talk to each other on local-first principles.
The future
Applying it to the design of the web we aim to create a system where we can do everything offline and in local networks and the connection to the internet is optional. This will help the neuronal groups be more resilient and fast. We invite others to join as co-creators to build a local first version of the Internet together.
The future will be the one you build.
Sources
- Marshall McLuhan. Understanding Media, 1964.
- New Directions in Cryptography, 1976.
- Conflict-free Replicated Data Types (CRDTs), 2011.
Originally published on Anytype - the everything app for those who celebrate trust & autonomy.

